The following lines are the result of collaborative work, under the leadership of Justin Seitz. There are many of us working together, including Heartbroken and Nanardon.
OSINT is an acronym for Open Source Intelligence. It’s a set of investigative techniques, allowing information to be retrieved from so-called open sources. Used by journalists, by police or in cybersecurity, OSINT can help to find information but it can also be used to protect yourself from malicious people.
Violences against people, especially against women increased and diversified. Harassment, raids, doxxing, revenge porn by video or by pictures, identity theft or school harassment, etc.
How to react? How to prevent them? Our goal is to give you simple resources, without the needs for special knowledge.
It doesn’t substitute support groups, law enforcement, health professionals or lawyers.
We trust you.
You are not responsible.
Facts and situations we will use to illustrate ours kits are criminally and civilly repressed.
You are not alone.
The information provided in this article does not, and is not intended to, constitute legal advice; instead, all information, content, and materials available in this article are for general informational purposes only. Furthermore this article was written mainly in regards to French and European laws. Readers should consult their local laws and contact an attorney to obtain advice with respect to any particular legal matter.
The word "dickpic" refers to unsolicited photos, showing genitals, sent by private message. Since it often involves penises, the term "dickpic" has been popularized.
The reasons why the authors of these contents send them remain unclear. Let it be clear in the reader's mind that we are talking about unwanted mailings and not about an exchange of personal photos, in a consensual and adult setting. Some people see it as a way of flirting, others do it to harass. Either way, it is still punishable and no person should receive unwanted graphic images.
In this article, we will talk about any unsolicited sending of sexual pictures or images of a sexual nature, regardless of the gender of the senders and recipients and the people photographed.
Photos sent by direct messages
In this case, we will talk about photos sent directly via an email application or a social network. This can be via Facebook, Twitter, Instagram, LinkedIn, Discord, Snapchat or Telegram, email or text message.
Attackers usually take advantage of the fact that victims have set up their accounts in such a way that they can receive messages from people they do not follow. Here again, we will refer to the previous methodologies, i.e. to record and archive from the article on digital raids and to lock one's accounts, explained in the article on doxxing.
In the particular cases of email or SMS, the sender has been aware of your identifiers, you may even have given them. This remains an offence and it is possible to block the sender by configuring filters.
Some victims, both French and American, have found a rather amusing parry. Since the attackers were generally not known for their quick-wittedness, they made it look like the messages had been directly transmitted to the police authorities via an application or filtered beforehand because they showed explicit content. For the moment, this type of application has not yet seen the light of day.
Obviously, even if they are private messages, you can report them to Facebook, Twitter, Instagram, etc. The procedure is almost the same as for public messages.
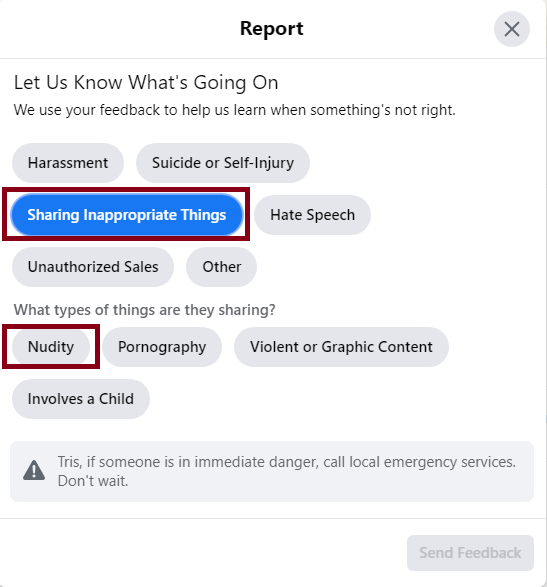
For Facebook, you have to report all conversation and not only a part of message. Click on the name and select “something’s wrong”.
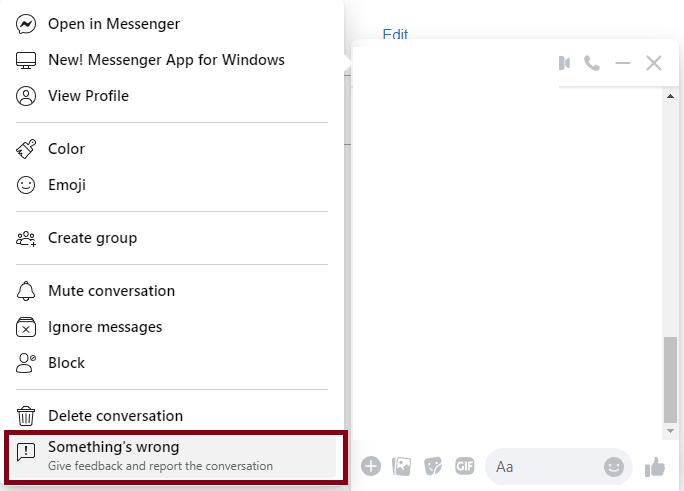
Choose “sharing inappropriate things” and “nudity”.
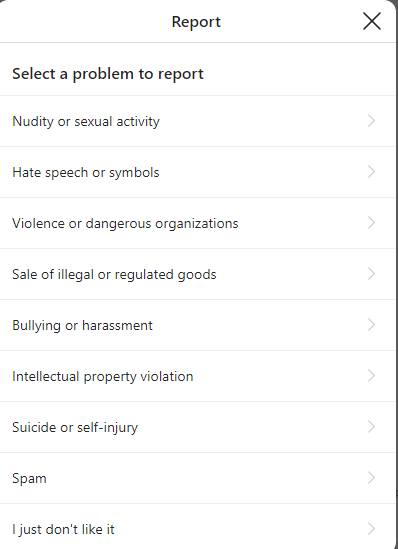
For Twitter, click near the message, select “report” and you will see same options as public tweet.
Instagram’s system is the simplest: just click on “report” near the message.
Is it necessary to practice the "name & shame", i.e. to reveal in the public square, the messages received? Victims will be advised against doing so. Indeed, even on a social network, it remains a private correspondence and ill-intentioned people could turn against the victims, relying on the secrecy of the correspondence.
The case becomes more specific when the recipients are minors. The penalty is increased, regardless of the legislation of the countries concerned. In the French case, it is a case of exhibitionism.
We will therefore think about activating the feature that allows you to receive a notification by email when someone sends you a private message, because it allows you to keep an additional trace.
Photos sent by a photo platform
This is rarer, but it does happen: the malicious person simply sends a photo, uploaded to a private album, for example Flickr. What should I do if the album has been deleted from the site? There is a parry. You should know that most of today's sites use what is called metadata to generate a preview of the content. So, on this site, if you right-click and then display the source, you'll find information, for example <meta name=" description " content=" The following lines are the result of a collaborative work, under the impetus of Justin Seitz. There are several of us working together, including Heartbroken and Nanardon. »/>. You can also find an online date, an overview of the illustrations used, keywords, etc.
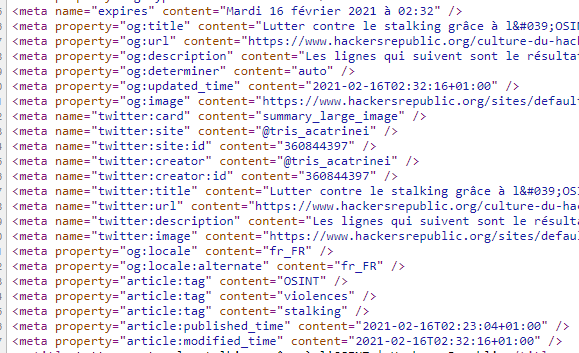
It turns out that most social networks, when sharing content, do not remove metadata. This means almost nothing in terms of storage. In the case of Facebook and Twitter, this information is always available. An experiment on this subject was conducted and published by Open Facto. The post is in French but you can translate it with DeepL.
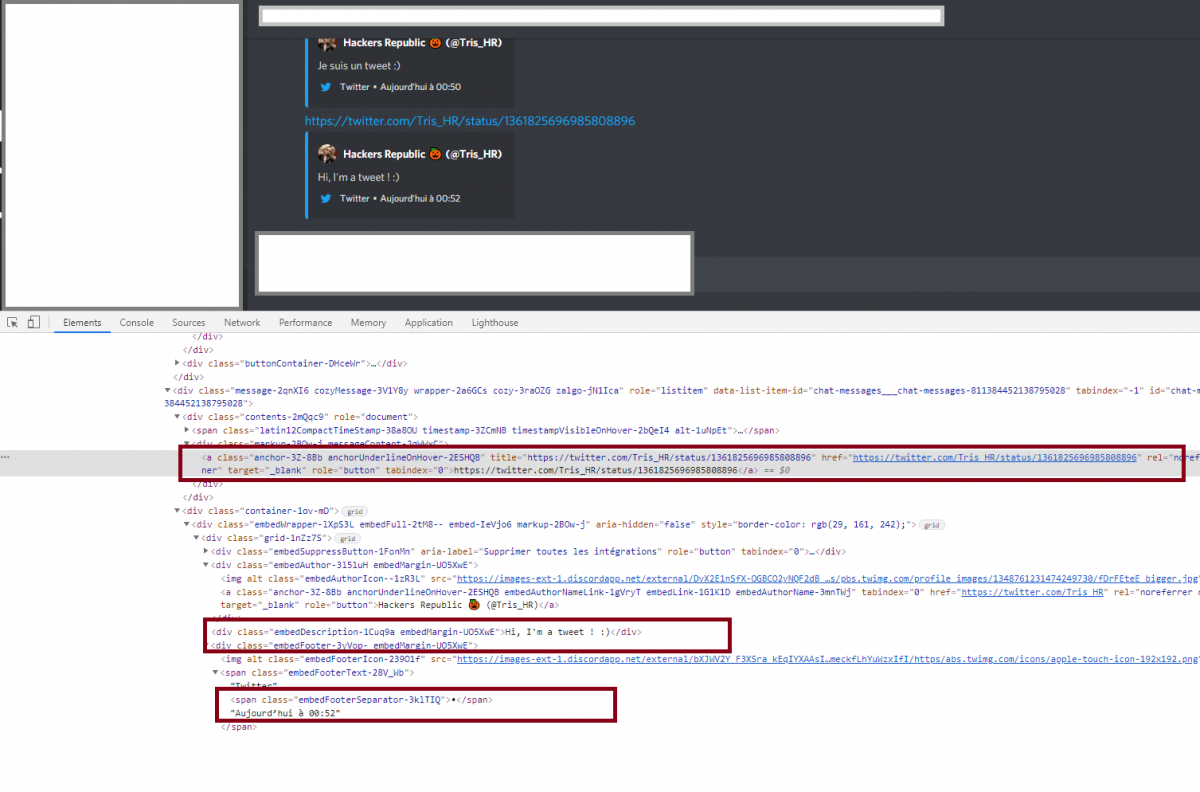
This is also true for Discord. For example, if you share a tweet in a Discord chat room and the tweet is deleted for a few moments, you will still see the text message.
So, if you receive photos, which have been hosted on a Flickr-like platform, feel free to send yourself a message on Messenger (Facebook) to keep not only the links, but also the metadata and photos.
On the other hand, be aware that social networks and some messaging tools remove EXIF data (associated data) from photos, for storage size reasons. If a photo is shared via Twitter, Facebook, Discord or other means, you'll be hard pressed to retrieve data such as geolocation, camera used or even the date the photo was taken.
The specific case of Discord
Discord is a kind of hybrid in communication tools, a mix between IRC (online discussion) and social networks. How to extract conversations? There is a very easy to use tool that allows you to fully download conversations, both private and in chat rooms. You will need to install a browser extension and then a specific script. From there, you will be able to fully download an entire chat room or conversation. The downloaded file is a text file, including the timestamp, the user id and of course the messages. The only negative point is that it can't load the content metadata we were talking about earlier, for example, tweets metadata. The tool also provides a viewer, to facilitate the reading of exchanges.
It may happen that Discord detects the archiving scripts and take you for a robot. Use this tool sparingly so as not to be banned from the tool.
Should I take legal action for such content? As said before, every victim is different. You are free to sue if you wish. Beyond the fact that it is a crime in many countries, most people who engage in this type of behavior do not make only one victim. It is a serious offense in most countries to possess or transmit photographs of minors, and if you suspect you have been sent imagery of children you should report it to the platform immediately.
Ajouter un commentaire