The following lines are the result of collaborative work, under the leadership of Justin Seitz. There are many of us working together, including Heartbroken and Nanardon.
OSINT is an acronym for Open Source Intelligence. It’s a set of investigative techniques, allowing information to be retrieved from so-called open sources. Used by journalists, by police or in cybersecurity, OSINT can help to find information but it can also be used to protect yourself from malicious people.
Violences against people, especially against women increased and diversified. Harassment, raids, doxxing, revenge porn by video or by pictures, identity theft or school harassment, etc.
How to react? How to prevent them? Our goal is to give you simple resources, without the needs for special knowledge.
It doesn’t substitute support groups, law enforcement, health professionals or lawyers.
We trust you.
You are not responsible.
Facts and situations we will use to illustrate ours kits are criminally and civilly repressed.
You are not alone.
The information provided in this article does not, and is not intended to, constitute legal advice; instead, all information, content, and materials available in this article are for general informational purposes only. Furthermore this article was written mainly in regards to French and European laws. Readers should consult their local laws and contact an attorney to obtain advice with respect to any particular legal matter.
One of the side effects of digital raids, which are accompanied by doxxing, can be identity theft. Attackers look for anything they can find on a victim and databases that have been hacked and leaked.
When we talk about online identity theft, we are talking about two main things:
- Social network account impersonation;
- The usurpation of "real" identities.
These two hypotheses are neither exclusive nor exhaustive, but they are frequently encountered.
The usurpation of social network accounts
This is the case when someone is pretending to be you on social networks or worse, has stolen your account. How is this possible? Sometimes the password is just too simple to guess.
Most of the time, the login or password is somewhere “into the wild” and the victims use the same couple of id and password. There are services that allow you to find out if the password associated with an email address has been found.
The Have I been pwnd service can help you determine if you have been a victim of a data leak. If your email is nowhere, here's what will be displayed.
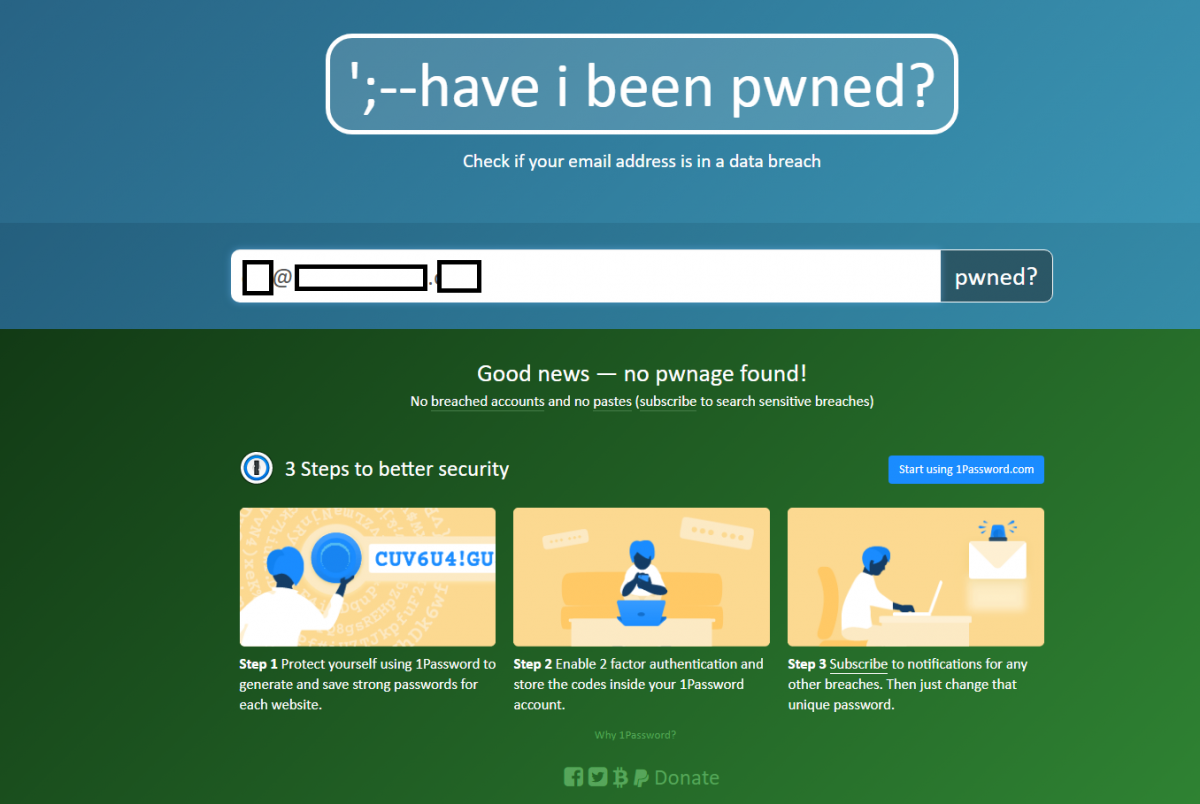
Conversely, if your email is in a database that has been compromised, here is the result.

You have to change your password and of course: a site = a different password.
This is often how malicious people manage to hijack network accounts. They use the person's password to connect to their mailbox, then to the accounts, change the passwords, phone numbers and the victim is left without their accounts.
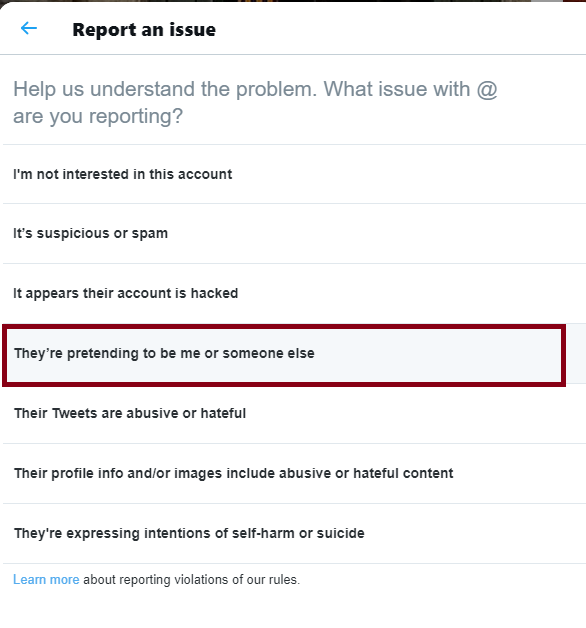
On Twitter, all you have to do is report the account.
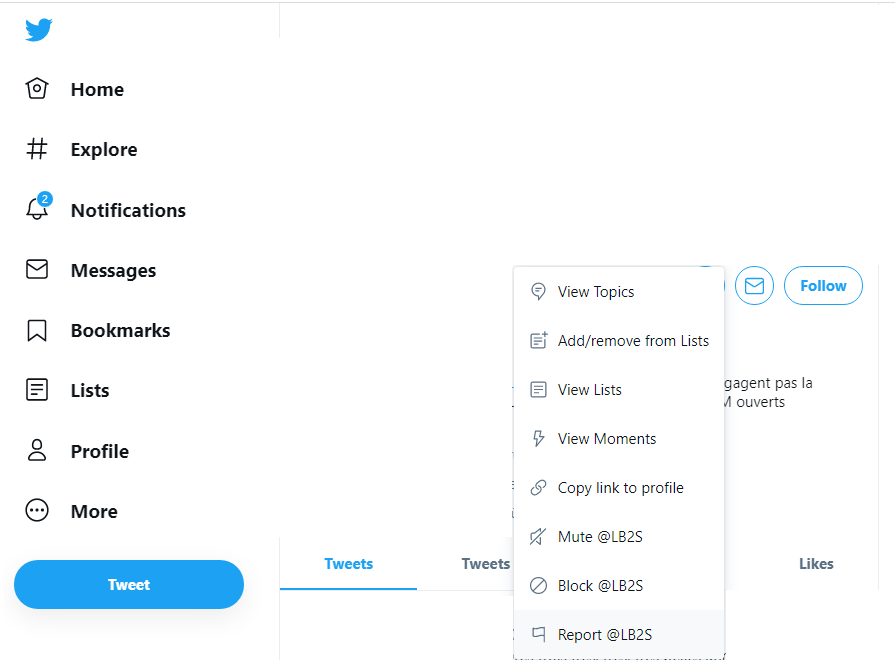
Go to "report" and then "he's pretending to be me". You will be asked for details and possibly to prove that you are the rightful account holder.
On Facebook, the process is almost the same.
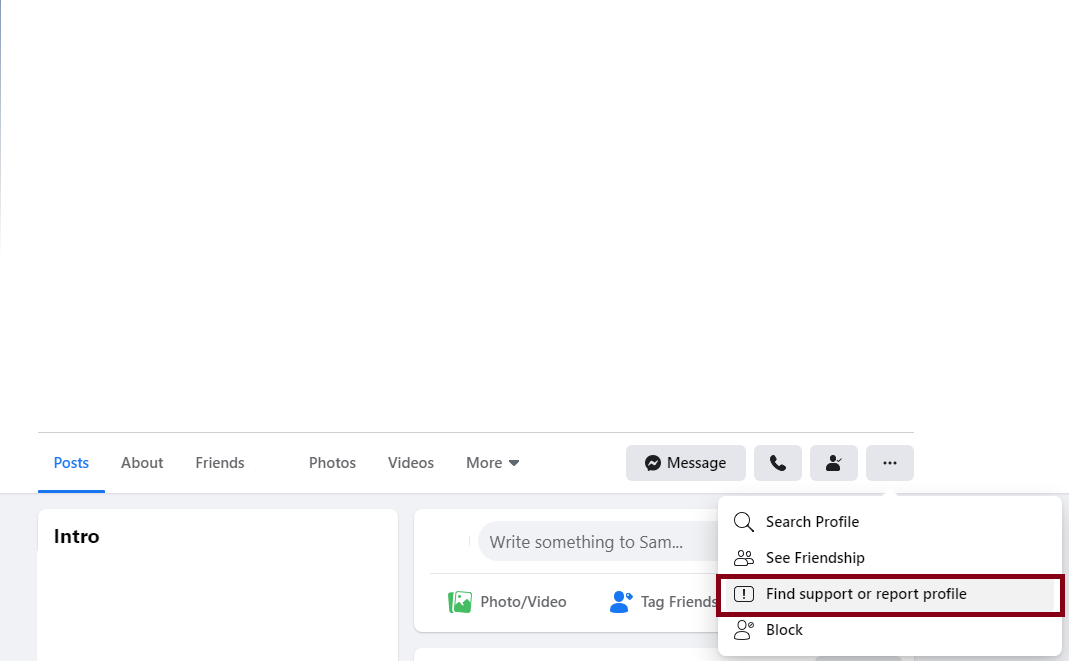
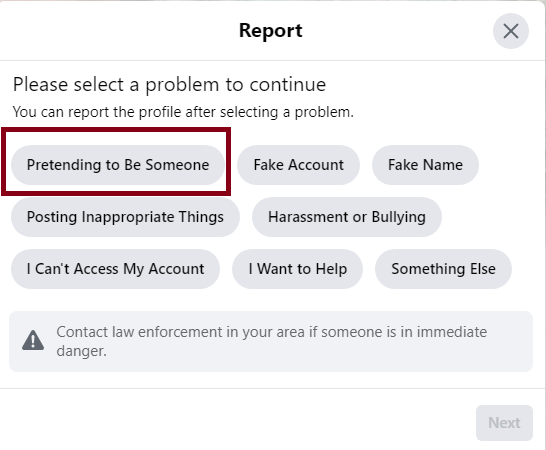
Choose "find support or report profile" and then, click on "pretending to be someone".
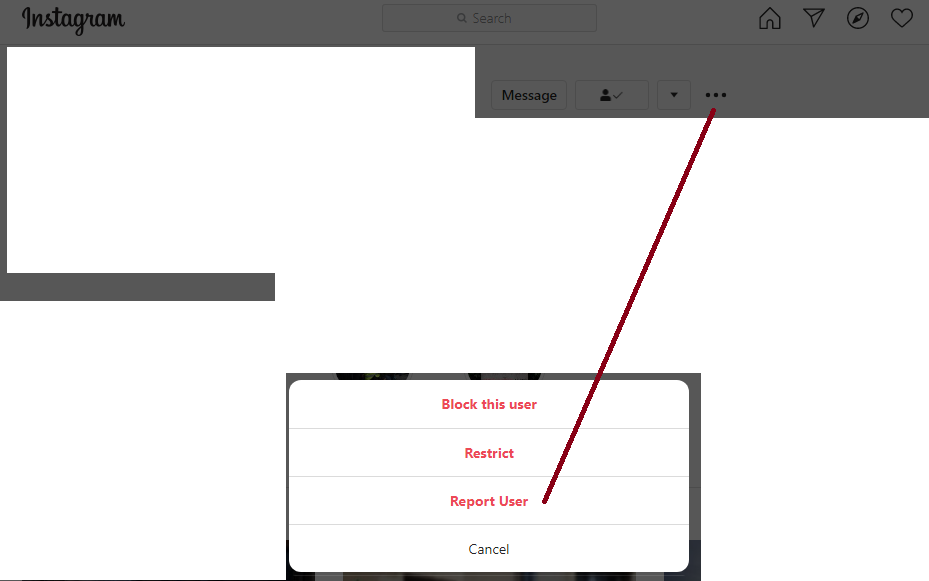
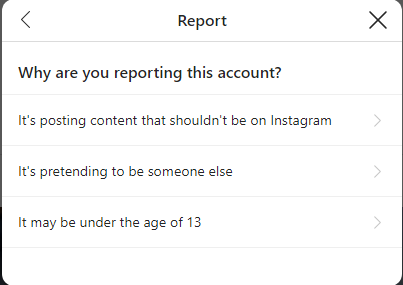
On Instagram, choose "report user"
Then "it's inappropriate".
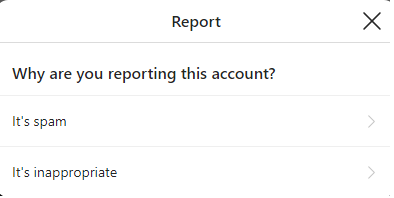
Than "report account".
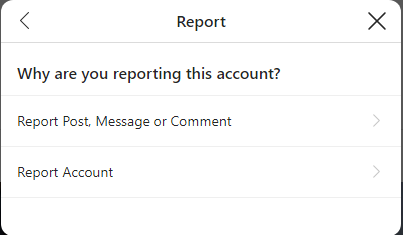
And, finally "it's pretending to be someone else".
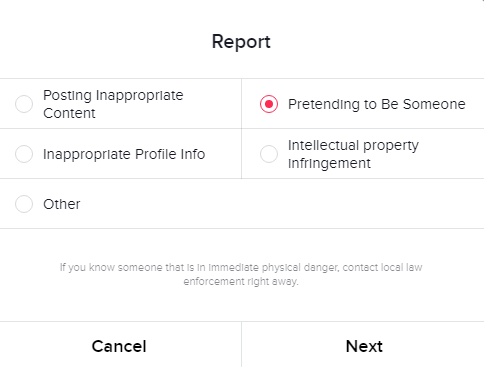
On TikTok, here again, the procedure is simple: first, click on "report".
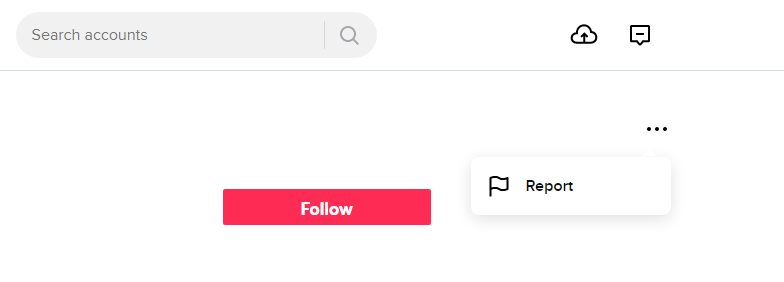
Then, "report account".
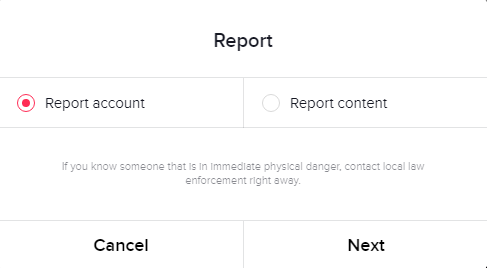
And finally, choose "pretending to be someone".
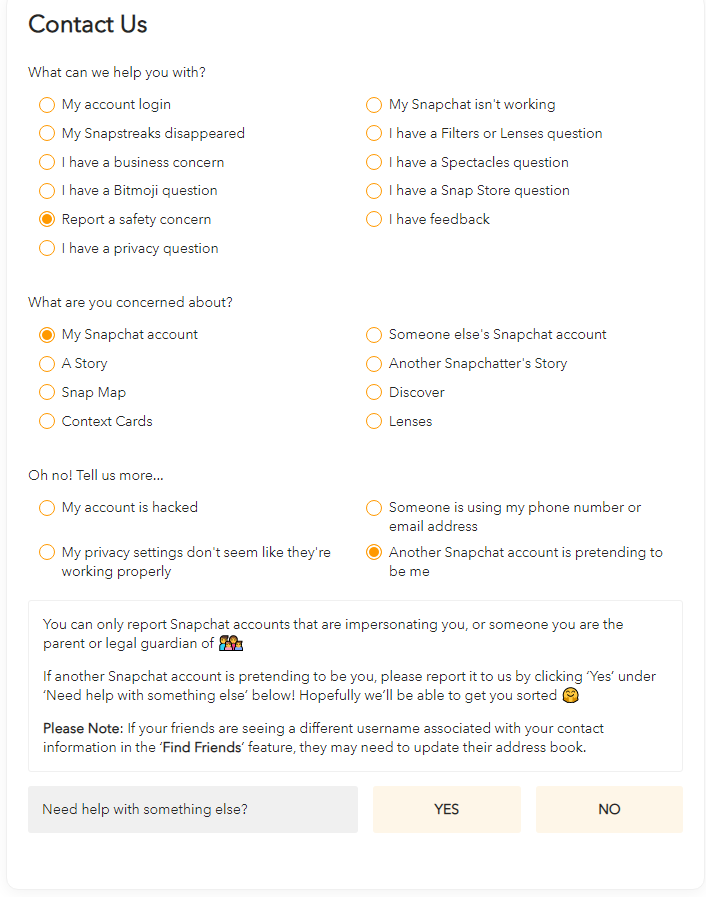
For Snapchat, there is a dedicated form . You select "report a security problem" then "my Snapchat account" and finally "my account has been hacked" or "someone is using my phone number or email address" or "another Snapchat account is pretending to be me" as the case may be.
Regarding Discord, there does not appear to be any specific procedure for reporting account hacking.
“Real" identity theft
When we talk about "real" identity theft, we are referring to cases where the attacker has access to very sensitive information about a person: his social security number (for Americans), bank cards, a telephone number and all the data that could steal your identity or impersonate you at banks or social agencies.
Block your bank cards, notify the official organizations with a letter as well as your professional, friendly and family entourage. Also file a complaint to the police.
What about the usurpation of mailboxes? For Gmail, here and for Hotmail, here. You will have to be patient. If your mailbox is that of your Internet service provider, contact them directly by phone.
The protean identity theft
We think about it much less, but it can happen that a malicious person uses different elements of different people to build a totally invented identity. For example, using only a person's photos, but not their identity, or even their postal address, email, first and last name, to build a completely invented character.
This is one of the almost impossible cases to prevent. No matter when you find out, it will be too late. The only existing parry is to make reverse image, in a very regular way, on your own photos.
In the second part of our kit, we will explain how to prevent this kind of inconvenience as much as possible. Finally, be aware that no matter the state and no matter whether it is digital or real identity, identity theft is a crime, usually criminal, often a misdemeanor. Here again, do not hesitate to file a complaint, both criminal and civil.
Ajouter un commentaire